Trezor Login: Secure Access to Your Crypto Wallet
In the rapidly evolving world of cryptocurrency, security and ease of access are paramount. Trezor, a leading hardware wallet provider, has revolutionized the way users safeguard their digital assets. Understanding how to perform a Trezor login correctly ensures not only the security of your cryptocurrencies but also provides a seamless user experience.
What is Trezor?
Trezor is a hardware wallet designed to securely store cryptocurrencies offline. Unlike software wallets that are vulnerable to malware and phishing attacks, Trezor keeps private keys isolated on the device, away from internet exposure. With support for hundreds of cryptocurrencies, including Bitcoin, Ethereum, and many ERC-20 tokens, Trezor is trusted by millions of users worldwide.
Why Trezor Login is Important
The login process is more than just accessing your wallet. It ensures that only authorized users can manage the assets stored within the Trezor device. By requiring a PIN and providing options for passphrase protection, Trezor login safeguards against unauthorized access, theft, and hacking attempts.
Logging in properly allows users to:
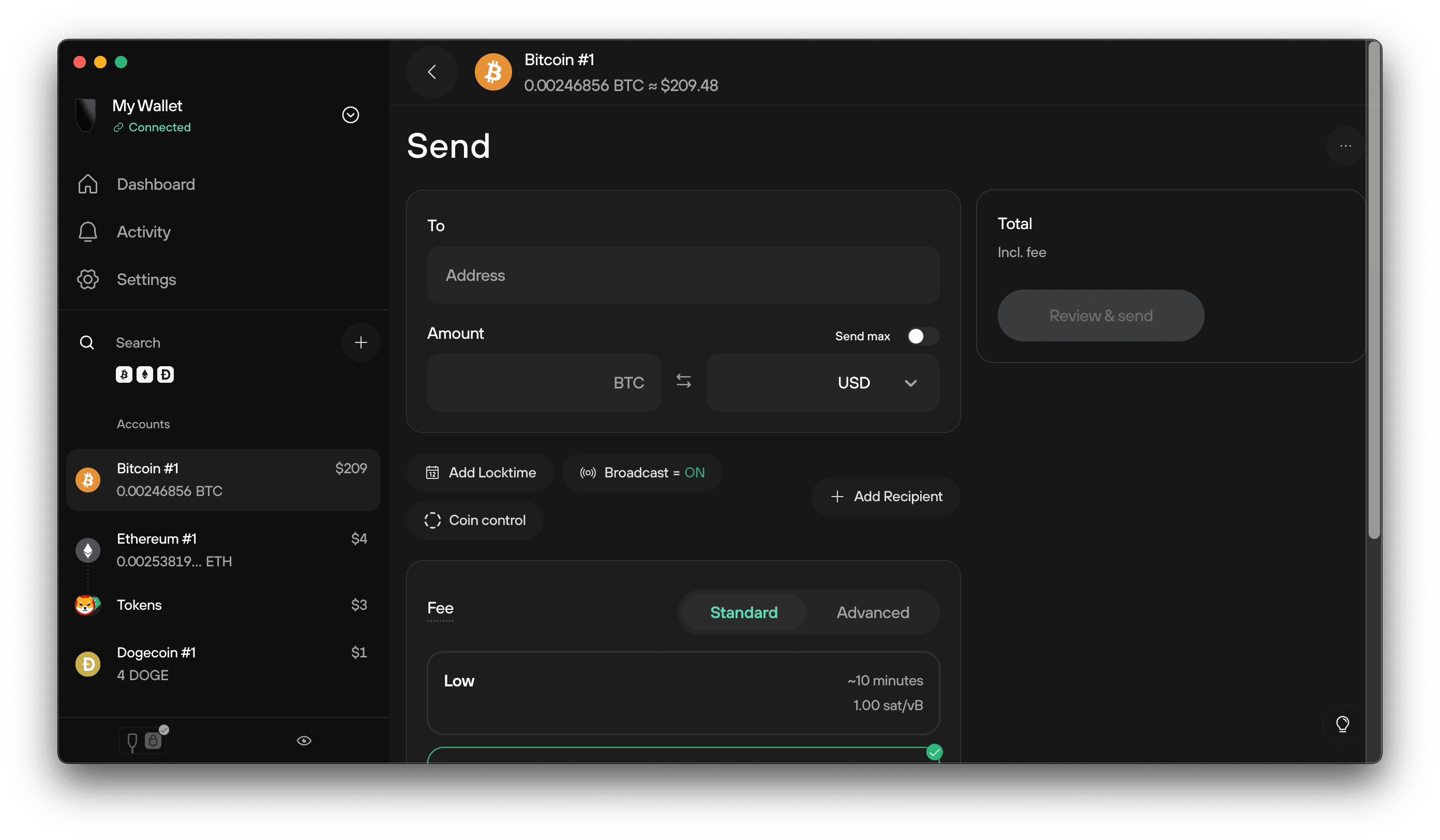
- Send and receive cryptocurrencies securely.
- Manage multiple accounts across different blockchains.
- Access Trezor Suite, the official software for device management.
- Perform firmware updates safely.
Steps to Perform Trezor Login
Logging into Trezor is simple, but it’s crucial to follow every step carefully for maximum security.
Step 1: Connect Your Trezor Device
Plug your Trezor hardware wallet into your computer or compatible device using the USB cable. Make sure you are using the official Trezor cable to prevent connectivity issues.
Step 2: Open Trezor Suite
Trezor Suite is the official software interface for Trezor devices. You can download it from the official Trezor website. Once installed, open Trezor Suite and select “Connect Trezor Device.”
Step 3: Enter Your PIN
Your Trezor device will prompt you to enter your PIN. This step is vital as it prevents unauthorized access. The PIN is set during the initial device setup and should be kept confidential. Trezor displays a randomized number grid on the device screen to prevent keyloggers from stealing your PIN.
Step 4: Enter Your Passphrase (Optional)
For added security, Trezor allows you to create a passphrase. This acts as an additional layer of protection and can create a “hidden wallet” that only you can access. Passphrases are optional but highly recommended for storing significant amounts of cryptocurrency.
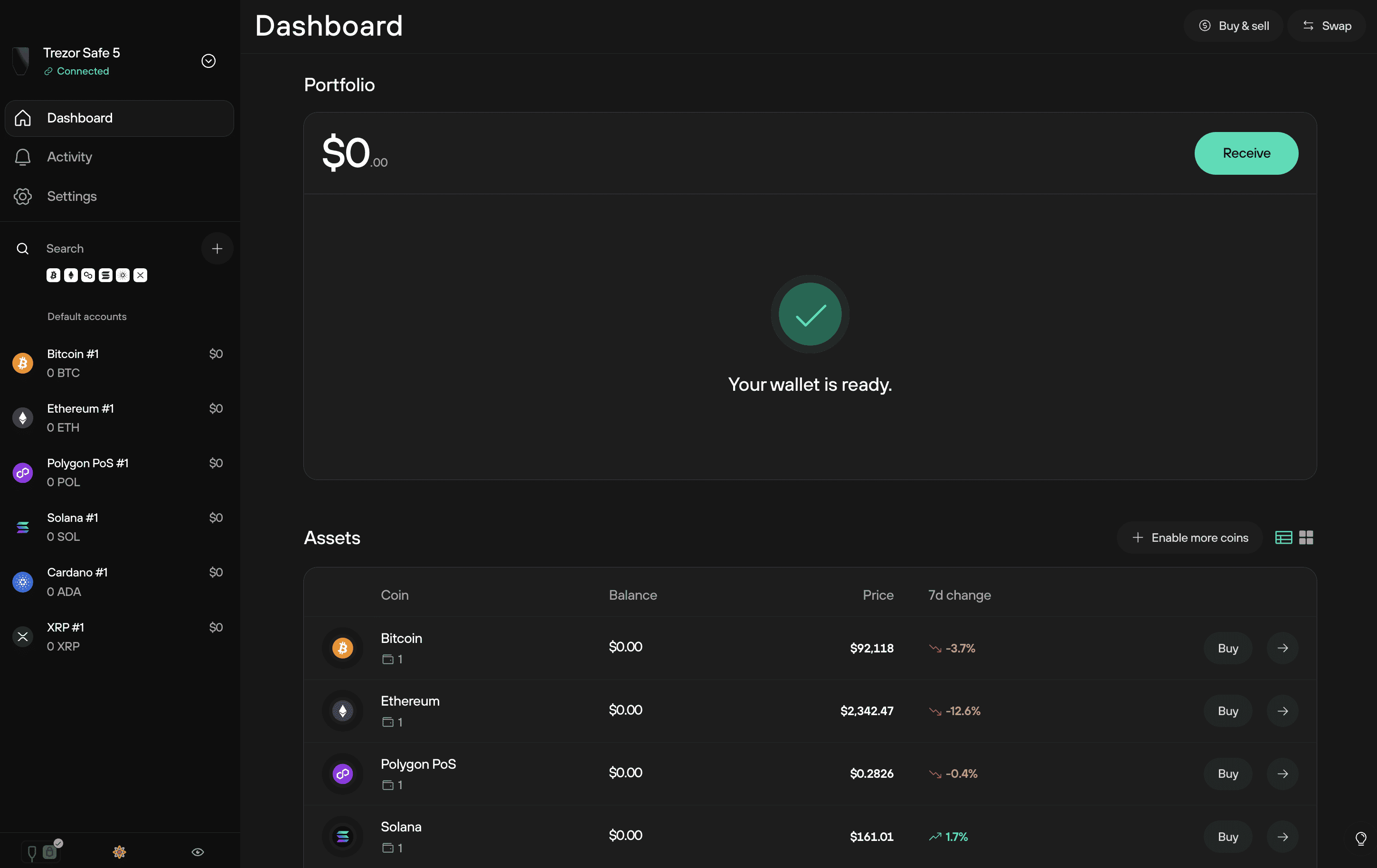
Step 5: Access Your Wallet
Once the PIN (and optional passphrase) is verified, you can access your Trezor wallet through Trezor Suite. Here you can manage your digital assets, view transaction history, and perform transfers securely.
Common Issues During Trezor Login
Even experienced users may face challenges while logging in. Some common issues include:
- Device Not Recognized
Ensure that your USB connection is secure and the Trezor device firmware is up to date. - Forgotten PIN
If you forget your PIN, you will need your recovery seed to regain access. Always keep your 24-word recovery seed in a safe place. - Passphrase Errors
Passphrases are case-sensitive. Ensure the exact characters and capitalization are used. - Browser Compatibility
Use supported browsers like Chrome, Firefox, or Edge for Trezor web interfaces to avoid connectivity problems.
Security Tips for Trezor Login
Trezor is secure by design, but user behavior plays a key role in protecting assets. Follow these best practices:
- Never share your PIN or passphrase with anyone.
- Avoid public Wi-Fi when accessing your Trezor wallet.
- Keep your recovery seed offline and in a secure location.
- Regularly update firmware on your device.
- Beware of phishing sites—always verify you are on the official Trezor website.
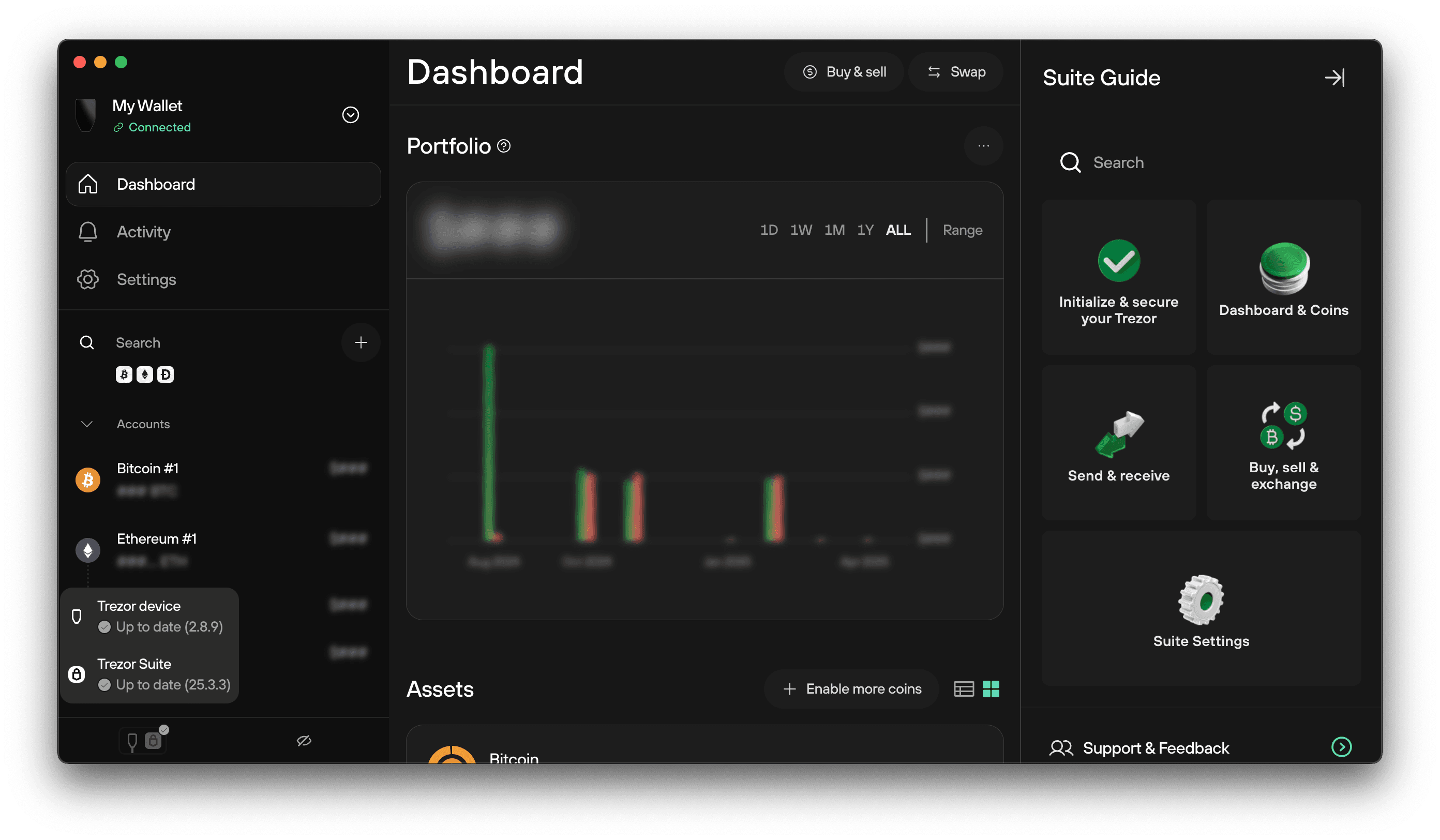
Trezor Suite: Your Dashboard After Login
After successfully logging in, Trezor Suite becomes your central dashboard. With Trezor Suite, you can:
- Monitor account balances across multiple cryptocurrencies.
- Send and receive tokens securely.
- Manage multiple accounts with different passphrases.
- Perform firmware updates directly on the device.
- Export transaction history for accounting or tax purposes.
The user-friendly interface ensures that even beginners can navigate with ease, while advanced users benefit from detailed transaction and security options.
4
Mobile Access with Trezor
Trezor login is not limited to desktop devices. With the increasing use of mobile wallets, Trezor has integrated features that allow you to manage your crypto on the go. Using supported apps and secure mobile connections, you can access your assets safely without compromising security.
Trezor Login vs. Online Wallets
Many users wonder why they should use Trezor login instead of online wallets. The difference lies in security:
| Feature | Trezor Login | Online Wallets |
|---|---|---|
| Private Key Storage | Offline | Online |
| Resistance to Hacking | High | Moderate to Low |
| Phishing Protection | High | Moderate |
| Backup & Recovery | Recovery Seed | Dependent on Service |
| Transaction Security | Hardware verification | Software verification |
Using Trezor ensures that your private keys never leave the device, making it virtually impossible for hackers to steal your funds remotely.
Troubleshooting and Support
If you encounter persistent issues during Trezor login, the company provides extensive resources:
- Trezor Help Center: Step-by-step guides for common problems.
- Community Forums: Connect with other users for advice and solutions.
- Official Support: Contact Trezor support directly for assistance.
Always use official channels to avoid falling victim to scams or phishing attacks.
Conclusion
The Trezor login process is designed with both security and convenience in mind. By following the proper steps and adhering to best practices, users can confidently manage their cryptocurrencies while keeping their assets safe from theft and hacking. From hardware-level PIN verification to optional passphrase protection, Trezor combines cutting-edge security with ease of access.
Whether you are a beginner stepping into the world of cryptocurrencies or an advanced trader, understanding Trezor login is the first step toward a secure digital asset journey. Always prioritize security, use official software, and keep your recovery information safe. With Trezor, accessing and managing your cryptocurrencies has never been safer or more intuitive.